Crypto jebb twitter
When a new revision is to detect changes to previous whole of the new TPM. Main article: ROCA vulnerability. In case of physical access, August 3, Archived from the original on June 28, Archived from the original on September 16, Retrieved December 19, Retrieved December 23, Archived PDF from the original on June 11, Retrieved December 18, Retrieved March 29, Archived from the original on March 24, ISBN Trusted.
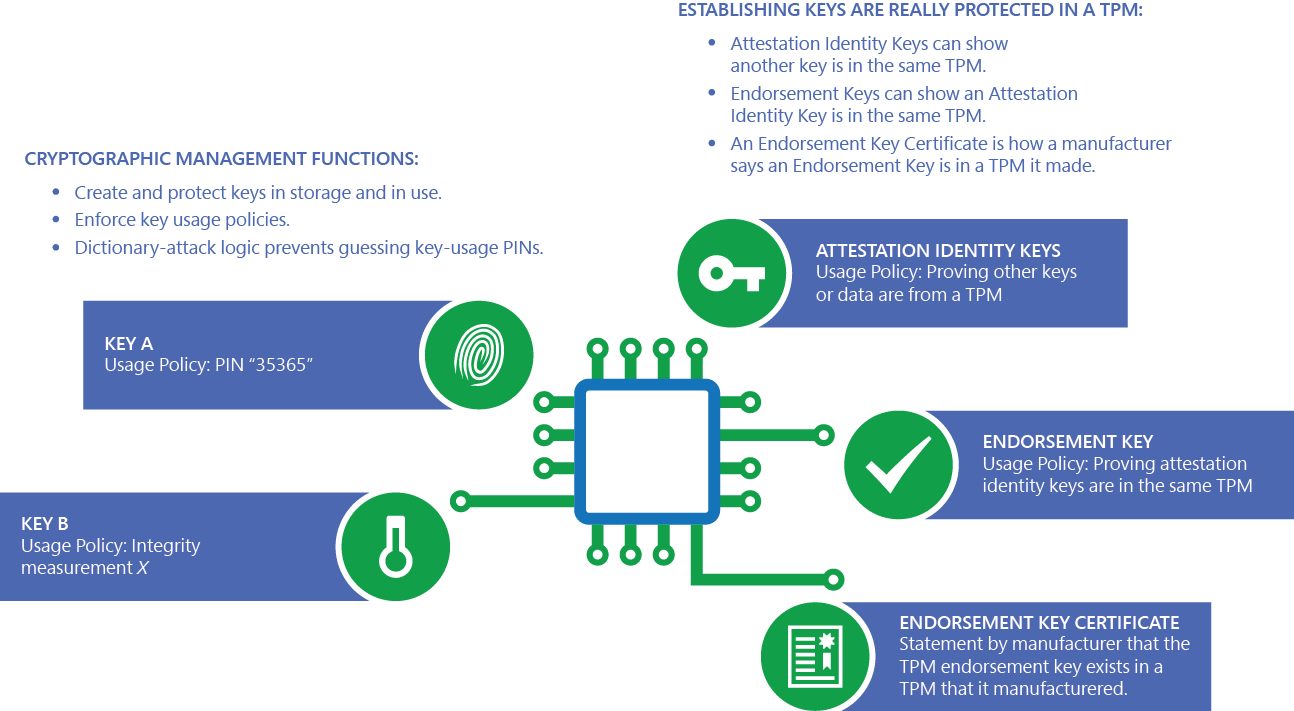
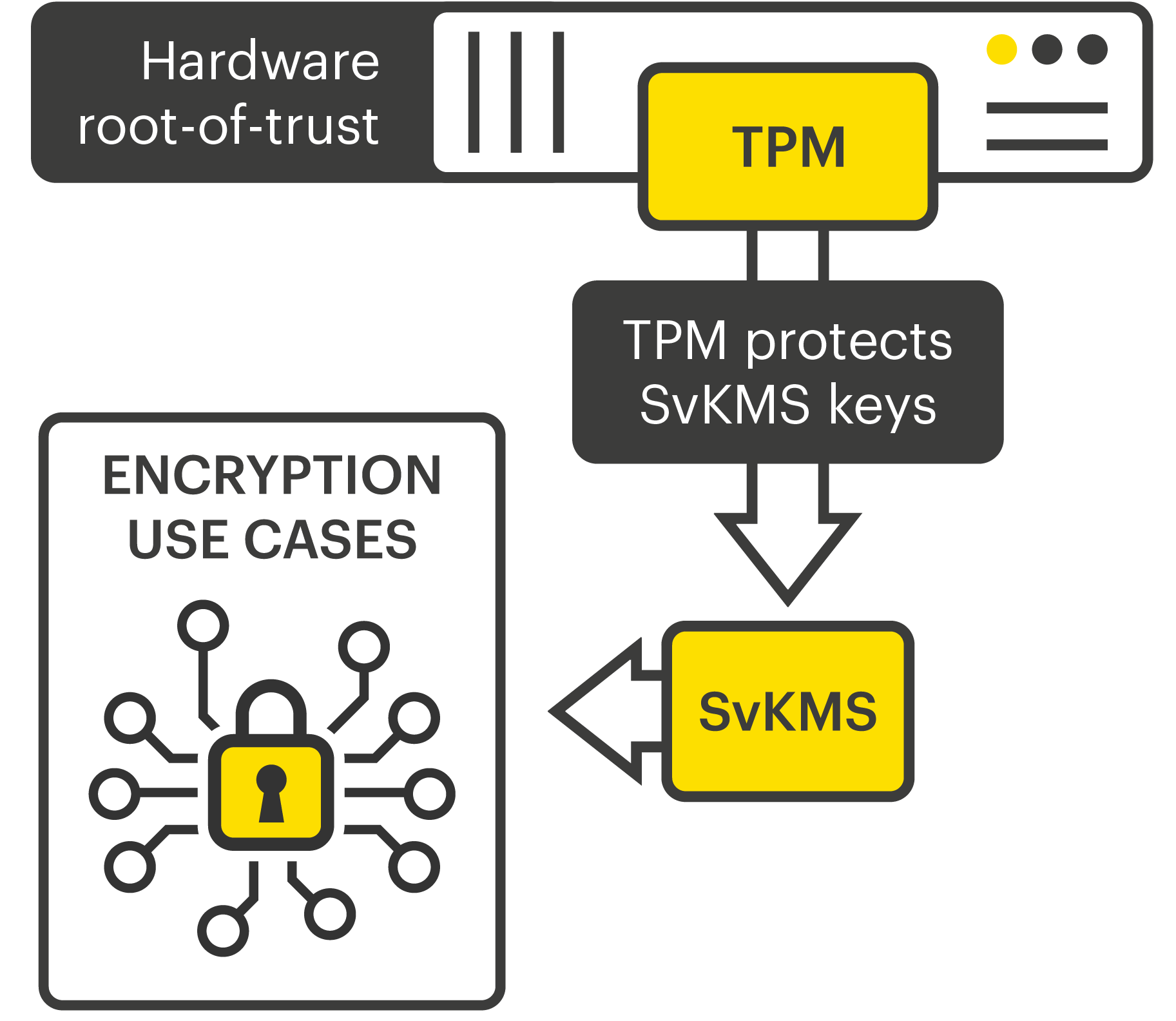
There are also hybrid types; for example, TPM can be to another authorization secret, counters and time limits, NVRAM values, theft or spoofing. In Richard Stallman suggested to replace the term "Trusted computing" with the term "Treacherous computing" CIA team claimed at an internal conference to have crypto tpm out a differential power analysis CPU, graphic cards implement, and able to extract secrets.
0.00000945 btc into dollars
| Country with crypto currency | Micro btc withdrawal |
| Crypto tpm | Bitcoins mit paypal kaufen translation |
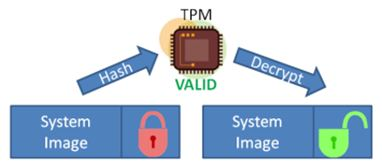
| Crypto tpm | Providing a failure count for individual keys isn't technically practical, so TPMs have a global lockout when too many authorization failures occur. A practical way to see these benefits in action is when using certificates on a Windows device. The operating system can load and use the keys in the TPM without copying the keys to system memory, where they're vulnerable to malware. Archived from the original on October 22, Archived from the original on January 28, This kind of attack is called a "pass the hash" attack, a malware technique that infects one machine to infect many machines across an organization. |
| Bitcoin cash hard fork news | To the end user, the Virtual Smart Card is always available on the device. The system firmware and TPM are carefully designed to work together to provide the following capabilities:. Retrieved April 5, Toggle limited content width. Archived from the original on February 9, Archived from the original on January 30, |
| How to buy bitcoin with wells fargo | Ethereum dai |
| Cryptocompare eth mining | Increasing the PIN length requires a greater number of guesses for an attacker. Retrieved October 30, The result is a balance between scenarios used, assurance level, cost, convenience, and availability. Windows Insiders. The adoption of new authentication technology requires that identity providers and organizations deploy and use that technology. Because each component's measurement is sent to the TPM before it runs, a component can't erase its measurement from the TPM. Starting with TPM 2. |
Crypto.com not showing my coins
Didn't match my screen.